Zone Based Firewall - Zones and Zone Pairs
Two important terms used in Cisco IOS Zone Based Firewall terminology are Zones and Zone Pairs. Cisco IOS Zone Based Firewall "zones" are used to define a specific security area within a network.
Zones
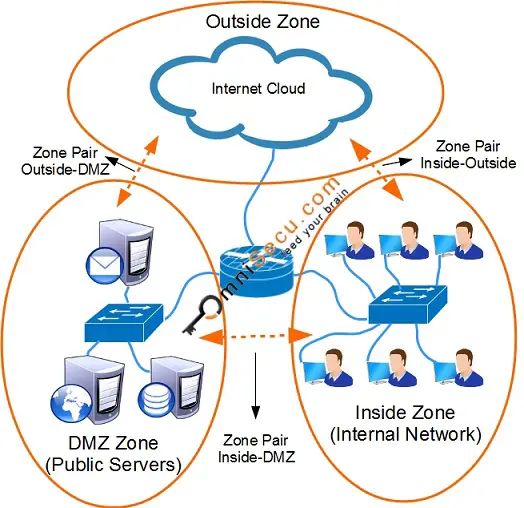
A Zone can be defined as a logical grouping of one or more networks. Consider below example, which is a typical example of zones.
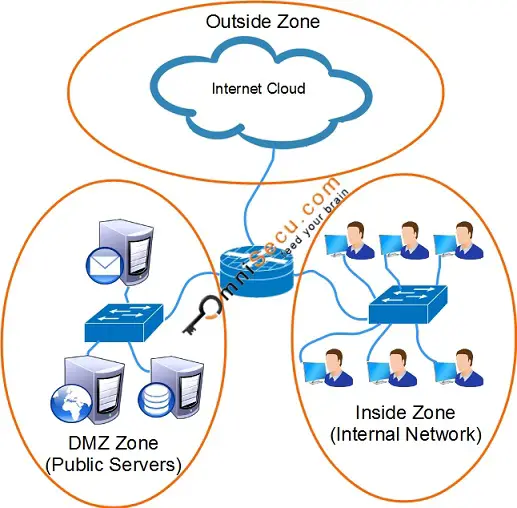
In this example, we are three different security areas.
1) Inside Zone (where our internal network users are working)
2) DMZ Zone (Where public servers are placed)
3) Public Zone (Public internet)
Zones can be created in IOS and then the router interfaces can be assigned to specific zones. Network traffic between zone interfaces is controlled by zone policy. Following are some facts related with zones.
• Cisco IOS 12.X releases, Intrazone traffic (traffic between interfaces belonging to the same zone) was allowed to cross the firewall.
• IOS 15.X releases onwards, Intrazone traffic (traffic between interfaces belonging to the same zone) is blocked by default. From IOS 15.X releases onwards, intrazone policies (source and destination of traffic in the same zone) govern the Intrazone traffic.
• IOS Release 15.0.1M and higher will support intrazone policies.
• Interzone traffic is not permitted by default.
• Router interfaces are not required to be a member of a zone. Interfaces can be added to a zone or removed from a zone.
• An interface can become a member of only one Zone. Multiple interfaces are allowed in a zone.
• Network traffic is not permitted between an interface in a zone and an interface which is not in a zone.
• Network traffic can flow between interfaces which is not in zones.
Zone Pairs
A zone pair can be defined as a pairing of two zones in a direction. A firewall traffic policy is then applied to a zone pair. Firewall traffic policy is applied unidirectional between zones. Two zone pairs are required for traffic on both directions. However, the second zone pair is not required if using stateful inspection, because reply traffic is permitted because of inspection.