What is Switch spoofing attack and how to prevent Switch spoofing attack
Before continuing, visit following links to learn what is Dynamic Trunking Protocol (DTP) and VLAN Hopping attack.
• What is DTP (Dynamic Trunking Protocol)
• Difference Between DTP "dynamic desirable" and "dynamic auto" Modes
• How to configure DTP (Dynamic Trunking Protocol) Modes
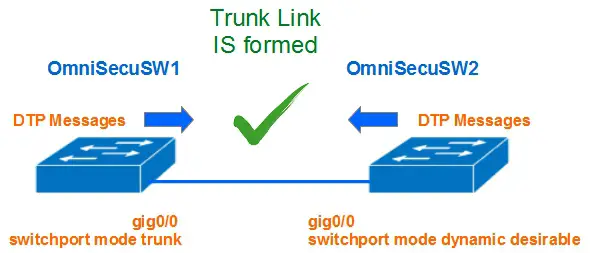
Dynamic Trunking Protocol (DTP) is used to dynamically build trunk links between two switches. "dynamic desirable", "dynamic auto" and "trunk" modes are used to configure an interface to allow dynamic trunking and frame tagging.
Switch spoofing is a type of VLAN hopping attack,
A switch interface which is connected to an end device (a computer or a printer) are normally in access mode and that end device will have access to its own VLAN. Traffic from other VLANs are not forwarded via that interface.
Consider a situation where an attacker is connected to a switch interface which is configured with either "dynamic desirable", "dynamic auto" or "trunk" modes. If the attacker can generate Dynamic Trunking Protocol (DTP) messages from his computer, a trunk link can be formed between his computer and the switch.
Another method of Switch Spoofing is by connecting a rogue switch to an interface configured with "dynamic desirable", "dynamic auto" or "trunk" modes.
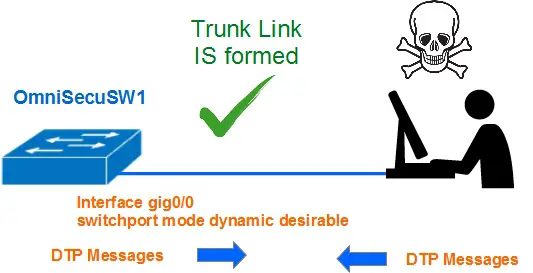
Once the trunk link is formed, the attacker can gain traffic from all the VLANs. The attacker can now sniff the traffic from all the VLANs.
How to prevent Switch Spoofing attacks
1) Never leave an access port in "dynamic desirable", "dynamic auto" or "trunk" mode.
2) Hardcode all the access ports as access port and disble DTP everywhere.
OmniSecuSW1#configure terminal OmniSecuSW1(config)#interface range gigabitethernet 0/0 - 20 OmniSecuSW1(config-if-range)#switchport mode access OmniSecuSW1(config-if-range)#switchport nonegotiate OmniSecuSW1(config-if-range)#exit OmniSecuSW1(config)#exit OmniSecuSW1#
3) Hardcode all the trunk ports as trunk port and never enable DTP on trunk ports.
OmniSecuSW1#configure terminal OmniSecuSW1(config)#interface range gigabitethernet 0/20 - 23 OmniSecuSW1(config-if-range)#switchport mode trunk OmniSecuSW1(config-if-range)#switchport nonegotiate OmniSecuSW1(config-if-range)#exit OmniSecuSW1(config)#exit OmniSecuSW1#
4) Shutdown all the interfaces which are not in use.