What are the terms Symmetric Encryption and Assymetric Encryption
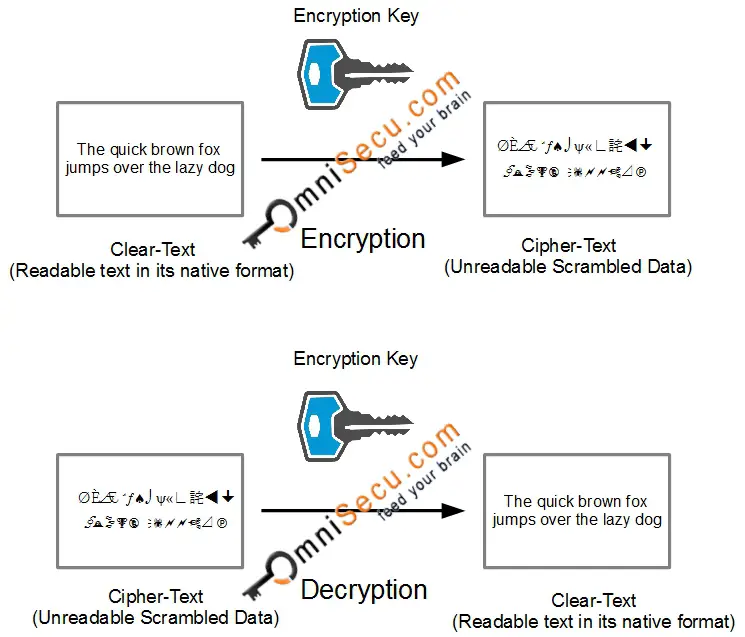
Symmetric Encryption is a type of Encryption where Clear-Text to Cipher-Text encryption and Cipher-Text to Clear-Text decryption are done using same Encryption Key. In other words, Symmetric Encryption is a process of converting Readable data (Clear-Text or Plain-Text) to Cipher-Text (Unreadable format) and converting it back to Clear-Text using same key. Symmetric encryption algorithms use the same key for encryption and decryption. The key must be exchanged so recipient so that data recipient can decrypt the Cipher-Text to Clear-Text and access the Clear-Text data.
The Clear-Text (Readable Text) is converted to Cipher-Text (Unreadable text) using an Encryption key. At the receiving end the same Key must be used to convert back the Cipher-Text (unreadable text) to Clear-Text (Readable Text).
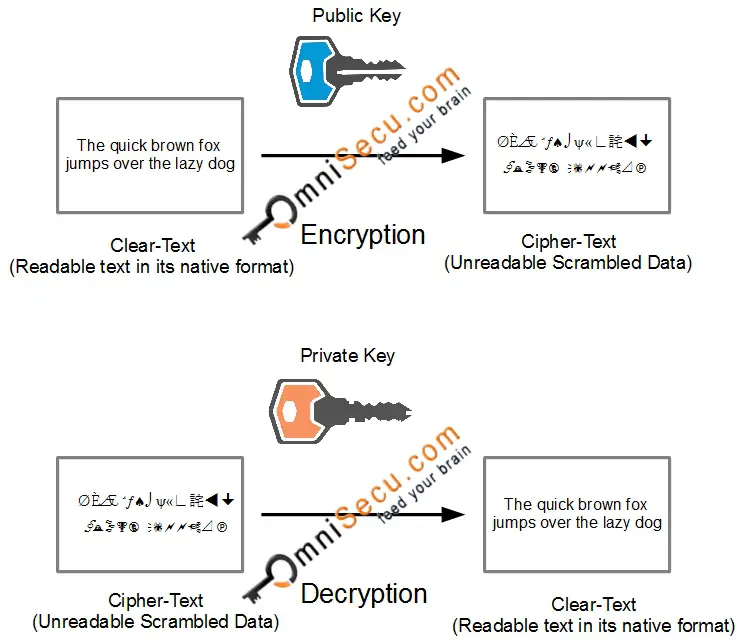
Asymmetric Encryption is more advanced than Symmetric Encryption and it increases the security of the encryption process by utilizing two separate, but mathematically related, keys known as a Public key and Private Key.
The most wonderful characters of Asymmetric Encryption Keys (Public Key and Private Key) are
• If Public Key is used for encryption, the associated private key MUST BE used for decryption.
• If Private Key is used for encryption, the associated public key MUST BE used for decryption
Note that encryption and decryption using the same key is not possible in Assymetric Encryption. The Private Key is possessed only by the user or computer that generates the Public/Private Key pair. The Public Key can be distributed to any person who wishes to send encrypted data to the Private key holder. It is impossible to compute the private key if you know the public key. Hence it is safe to publish the public key.