Active Directory Domain User Password Policy
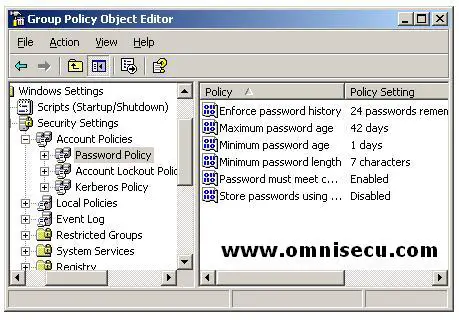
Password policies for Active Directory Domain user accounts and local user accounts are very important in implementing security and preventing unauthorized access to your Windows 2003 network. There are six important settings for password policies to control the management of Windows 2003 Active Directory Domain user accounts. These policies are located in domain group policy, Computer Configuration\Windows Settings\Security Settings\Account Policies\Password Policy.
To open the domain group policy settings, open Active Directory Users and Computers MMC snap-in (DSA.MSC), select Start > Administrative Tools > Active Directory Users and Computers or type DSA.MSC in the run dialog box and hit enter. Right clich the domain and select the "Properties" from the context menu. Select the "Default Domain Policy" inside the "Group Policy" tab, and click "Edit".
1) Enforce Password History: This setting is used to enforce Password History. By default, on a Domain Controller, value is 24 passwords, on a stand-alone server, the value is zero passwords. This means Windows 2003 will not allow the user to use 24 previous passwords which are in password history.
2) Maximum Password Age: The Maximum Password Age setting determines when users are required to change their passwords. For example, if this is set to 30 days, on the 31st day the user will be required to change his or her password. The default on domain controllers is 42 days. The value can be 0, which means that there is no limit.
3) Minimum Password Age: Minimum Password Age value determines how long users must use passwords before they are allowed to change the password.
4) Minimum Password Length: Minimum Password Length determines the minimum number of characters that makes the length of the password. This value should be kept high (8 or higher) for environments which require more security.
5) Password Must Meet Complexity Requirements: Password Must Meet Complexity Requirements determines how complex the domain password should be. If this policy is defined, passwords can’t contain the user account name, must contain at least six characters, and must consist of uppercase letters, lowercase letters, numerals, and special non-alphabetical characters.
6) Store Passwords Using Reversible Encryption: Store Passwords Using Reversible Encryption setting determines how the password is encrypted. By default, it is disabled on Windows Server 2003. Enabling this policy is similar as storing passwords as plain text and will decrease the password security much. This is only helpful when applications use protocols that require user’s password. Store Passwords Using Reversible Encryption setting should be used only when it is necessary.