How to configure static NAT in a Cisco Router
Static NAT (Network Address Translation) is one-to-one mapping of a private IP address to a public IP address. Static NAT (Network Address Translation) is useful when a network device inside a private network needs to be accessible from internet.
For example, we have a web server inside our network, which is configured with a private IP address as shown below.
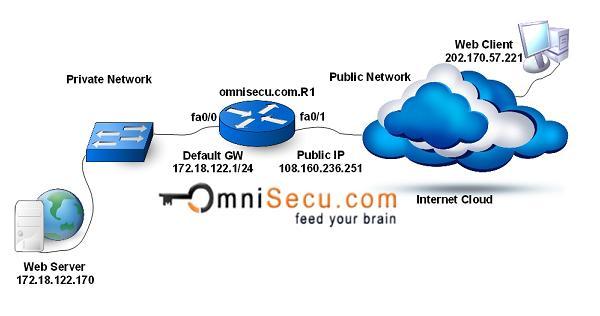
We want the to connect our web server with outside world, so that general public can visit our web pages. Our webserver is configured with IP address 172.18.122.170, which is a private IP address. The webserver is not directly accessible from the public internet because all the traffic originating from or destined to private IP addresses are dropped by public internet routers. Here static NAT can be used to allow forwarding traffic from the internet to a server inside our network with a private IP address. Generally, this technology is known as port forwarding.
When webclients try to make a connection to our webserver, they connect using a public IP address configured on our NAT (Network Address Translation) router (HTTP - TCP port number 80). The connection is then translated and send to the webserver. The HTTP response from the webserver is send back to the HTTP client.
The static NAT configuration command syntax for a Cisco Router is as below.
omnisecu.com.R1(config)#ip nat inside source static tcp <inside_local_ip_address> <inside_local_port> <inside_global_ip_address> <inside_global_port>
After configuring static NAT using above command, you have to identify which is the inside interface (facing the private network) and which is the outside interface (facing the public internet) using ip nat inside and ip nat outside from interface configuration mode.
The configuration commands are as below.
omnisecu.com.R1>enable omnisecu.com.R1#configure terminal Enter configuration commands, one per line. End with CNTL/Z. omnisecu.com.R1(config)#ip nat inside source static tcp 172.18.122.170 80 108.160.236.251 80 omnisecu.com.R1(config)#interface fa0/1 omnisecu.com.R1(config-if)#ip nat outside omnisecu.com.R1(config-if)#interface fa0/0 omnisecu.com.R1(config-if)#ip nat inside omnisecu.com.R1(config-if)#exit omnisecu.com.R1(config)#exit
Interface fa0/1 is the interface which is facing public internet and fa0/0 is the interface which is facing private inside network.