Software Restriction Policies
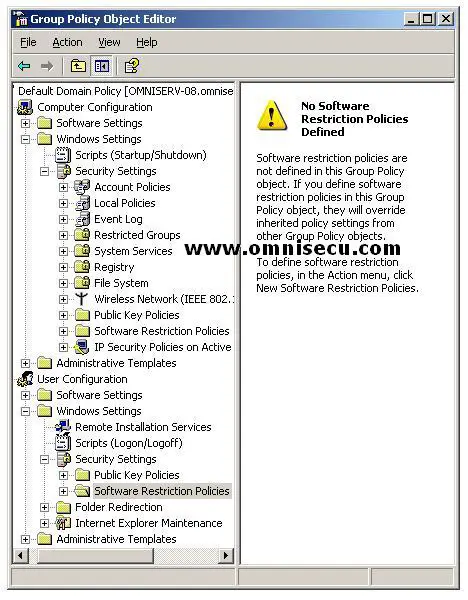
Software Restriction Policies in Windows 2003 provide a powerful mechanism for blocking software execution. In some particular situations, you might want to ensure that only the correct or genuine software are executed on your user’s systems. Software Restriction Policies are available in Group Policy for this purpose. Software Restriction policies are found in the Computer Configuration area or User Configuration area within Windows Settings\Security Settings\ Software Restrictions Policies.
Software Restriction Policies under Computer Configuration are used to set restrictions at computer level. Software Restriction Policies under User Configuration are used to set restrictions at user or user group level.
When we open the Software Restriction Policies node for the first time within a GPO, we can see a message on right pane that no software restriction policies have been defined. To start working with software restriction policies, right click Software Restriction Policies node and click Create New Policies from the context menu.
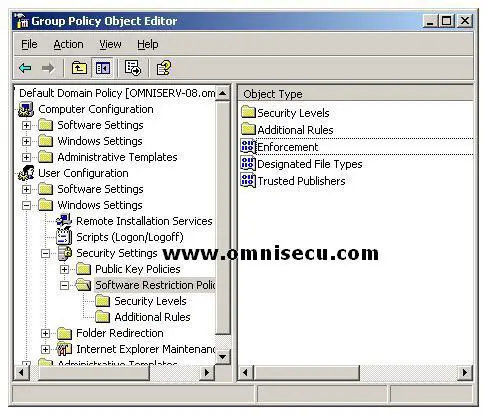
Following are the items shown in the right pane.
• Enforcement policy: Enforcement policy determines how software restriction is applied to software files and to whom software restriction applies.
• Designated File Types policy: Designated File Types determines what file types and extensions are considered to be executable code.
• Trusted Publishers policy: Trusted Publishers policy sets trusted software publishers.
• Security Levels node: Security Levels node contains policies that can be used to specify whether and how restricted software runs.
• Additional Rules nods: Additional Rules node contains policies that can be used to control software execution. We can create rules bases on
Hash Rule: We can create rules based on the hash value of the executable software. A "hash value" is a numeric representation that can uniquely identify a file. But, if any changes are made to the file, even one bit is changed; the hash value can be entirely different.
Path Rule: We can restrict certain applications based on path (where they reside on the hard drive). You can set up a Path rule to specify a specific folder or full path to a program.
Certificate Rule: We can use certificate rules to sign executable applications or scripts.
Internet Zone: We can specify which Internet Explorer zones are allowed for download. You can specify Internet, Intranet, Restricted Sites, Trusted Sites, and My Computer.