What is Double tagging attack and how to prevent Double tagging attack
Before continuing, visit following links to learn what is VLAN, native VLAN and VLAN Hopping attack.
Double tagging VLAN hopping attack is another type of VLAN Hopping attack. Double tagging attack will work only if the attacker is connected to an interface which belongs to the native VLAN of the trunk port. Double tagging attack is unidirectional.
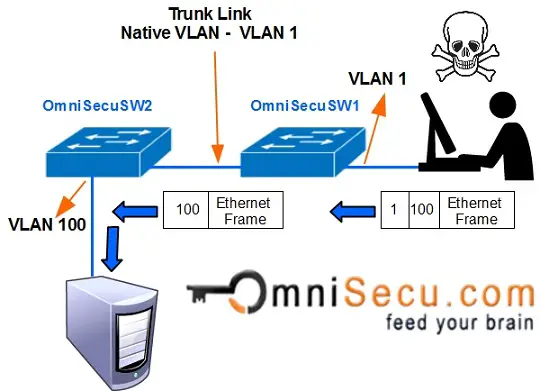
Double tagging VLAN hopping attack takes advantage 802.1Q tagging and tag removal process of many types of switches. Many switches remove only one 802.1Q tag. In Double tagging attack, an attacker changes the original frame to add two VLAN tags. An outer tag, which is of his own VLAN and an inner hidden tag of the victim's VLAN. Here the attacker's PC must belong to the native VLAN of the trunk link.
When the double tagged frame reaches the switch (OmniSecuSW1), the switch can only see the outer tag of the VLAN that the interface really belongs to.
The Switch OmniSecuSW1 will now remove the outer VLAN Tag and will forward to all the ports belong to native VLAN (in this example, VLAN1). One copy of that frame is forwarded to the trunk link to reach the next switch OmniSecuSW2.
When the frame reaches OmniSecuSW2, it will open the frame to see the second tag. OmniSecuSW2 will now assume that frame belongs to VLAN 100 and it is forwarded to VLAN 100.
How to prevent Double tagging attacks
Double tagging attacks can be prevented by keeping the native VLAN of the trunk ports different from the user VLANs.