What is token ring network
Token ring LAN Technology was developed by IBM in the middle 1980s as a fast and reliable alternative to Ethernet. Token ring technology used token passing to place data on media. Token Ring had a "Star Ring" topology. Token ring networks were physically similar to a Star Topology in appearance, but logically wired as a Ring Topology.
In a logical ring, there is a central device used to connect the network devices (Servers, Workstations, Printers, Scanners etc.) together. This central device was called as Multistation Access Unit (MAU). Multistation Access Unit (MAU) controlled a logical internal ring, using something called as ’Token’. Access to the network media for a network device is given only by the possession of a token that is passed from device to device on the ring.
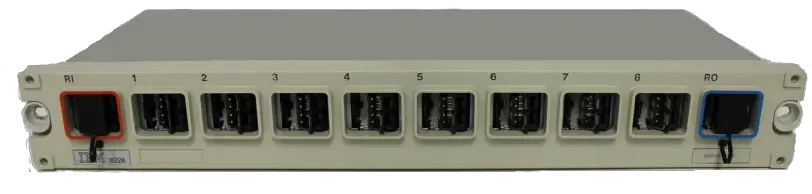
The central device which is used to connect the network devices is called as a Multistation Access Unit (MAU). Below image shows an IBM Multistation Access Unit (MAU)
Token-Ring based networks were more sophisticated and advanced than Ethernet, during the early days of networking. Token-Ring had a number of built-in diagnosis and correction mechanisms that helped in troubleshooting network problems. Collisions were not present in Token ring networks, as in early Ethernet networks. The main difference of Ethernet and Token ring is that, Ethernet uses Star Topology and Token ring uses logical Ring topology.
The basic concepts of Token passing are explained below.
A Token in Token ring network is a piece of information. A computer need to send data to network along with token. Token along with data is circulated to computers (or devices) in the network. When neighbor computer received token and data, it checks whether the data is addressed to it. If the data is addressed to it, that computer receives the data and passes the empty token back into the network. If the data is not addressed to it, that computer will pass the token and data to next computer, until the data reaches the destination computer.
When a Token-Ring network starts up, the devices take part in a negotiation to decide who will become the "Active Monitor". In Token-Ring network, "Active Monitor" is a machine with the highest MAC address and all other machines are 'Standby Monitors'. The job of the Active Monitor is to make sure that none of the machines are causing problems on the network, and to re-establish the ring after a break or an error has occurred.
A computer that passes the token to the next computer on the logical ring would be called the nearest active upstream neighbor (NAUN). The computer receiving the token is the nearest active downstream neighbor (NADN). Once a computer takes possession of the token and transmits data, it then creates a new token and passes it to its NADN.
Early Token-Ring networks had 4Mbps speed and later 16Mbps and 100Mbps speed Token-Ring networks were also available. Token Ring networks were replaced by Ethernet family technologies due to the advantages of Ethernet technologies.
These days, it is extremely difficult to find a business network operating using Token ring based LAN. Visit the below link to view the wikipedia Token ring page.