Why TELNET is not secure
The TELNET protocol was designed long back, even before the TCP/IP protocol suite. TELNET was initially designed for the computer networks of 1960’s and 1970’s, when networks were considered safe. TELNET traffic between a TELNET client and TELNET server is not encrypted, unless a third-party encryption tool or protocol is used.

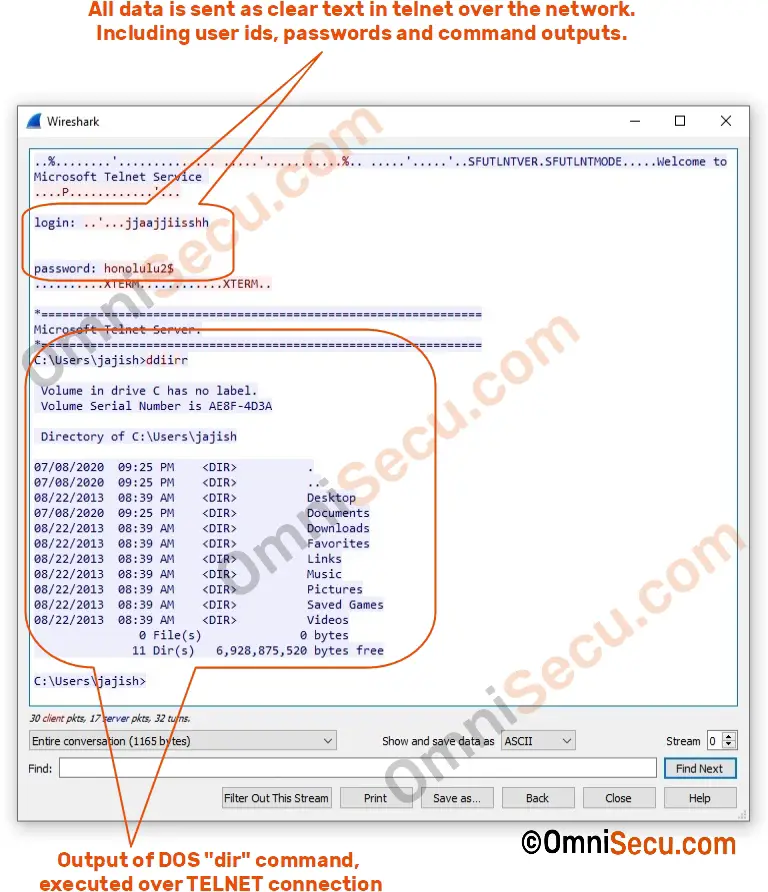
Data transfer between TELNET client and server, including login ids, passwords, commands and output, are in plain text. A malicious user who has access to the TCP/IP stream between TELNET client and TELNET server can capture the packets assemble the packets to get the user login ids and passwords.

A malicious user can view the command output also. Below image shows the captured user id, password and output of dir command executed over telnet. Command executed was DOS dir command, which shows the directory listing of the TELNET server.
Because this security reason, new Operating Systems are eliminating TELNET server. Windows 2019 doesn’t have an inbuilt TELNET server.